 Back to blog
Back to blog
In 2021, Microsoft required TPM 2.0 to install Windows 11. Millions of computers declared incompatible overnight. The press was outraged, forums overflowed with frustration, and TPM entered the public vocabulary with a disastrous image: an arbitrary obstacle invented to force hardware upgrades.
A deeply unfair reputation
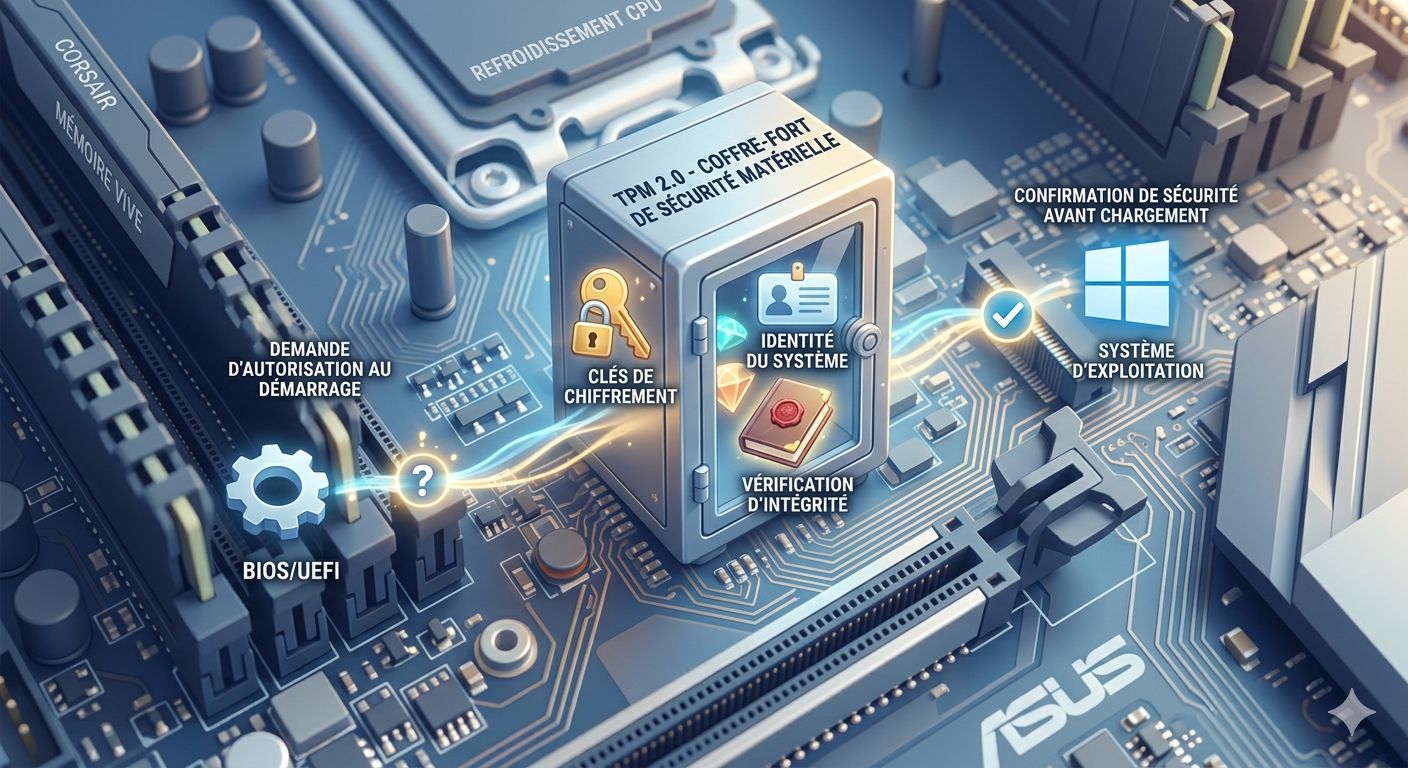
TPM is not a control tool. It is a hardware safe. Its role is simple: store sensitive cryptographic keys in a physical chip, isolated from the rest of the system. These keys cannot be extracted by software. They do not travel over the network. They only exist there, on that chip, on that machine.
You already use it every day
Android's hardware keystore, Apple's Secure Enclave — these are exactly the same principles. These chips protect your fingerprint, your payment keys, your biometric credentials on your phone. Nobody complains about it. Everyone benefits from it, without even knowing it.
TPM does the same thing on PC and Linux. It was just waiting to be used for what it truly is: a protection tool, not a barrier.
Lockystar and TPM
This is exactly how we use it at Lockystar: the user profile — which contains your private key — will soon be protected by the TPM chip on Windows and Linux. A hardware security layer, on machines that support it, so that your cryptographic identity can no longer be attacked offline.